In today’s connected world, digital activity leaves behind an evidence trail that could make or break an argument. The truth is often hidden in devices, accounts and data logs, whether it’s for a legal investigation or for a corporate data breach. But to uncover that truth, you need more than IT support. It requires precision, experience and legally sound practices.

Blueberry Security provides high-level cyber forensic services that are specifically designed to handle serious situations. Instead of relying on speculation or a lack of analysis, their focus is on the extraction of verified legal-required evidence that stands up under scrutiny.
Digital Forensics: Beyond the basics of IT
A lot of people turn to tech support for general assistance when their accounts have been compromised or suspicious activities are observed. While this can help restore access to the account, it’s not enough to provide answers to more complex questions. Who has accessed your system? What time did it occur? What information was affected? These are the critical facts that only experienced digital forensics experts can discover.
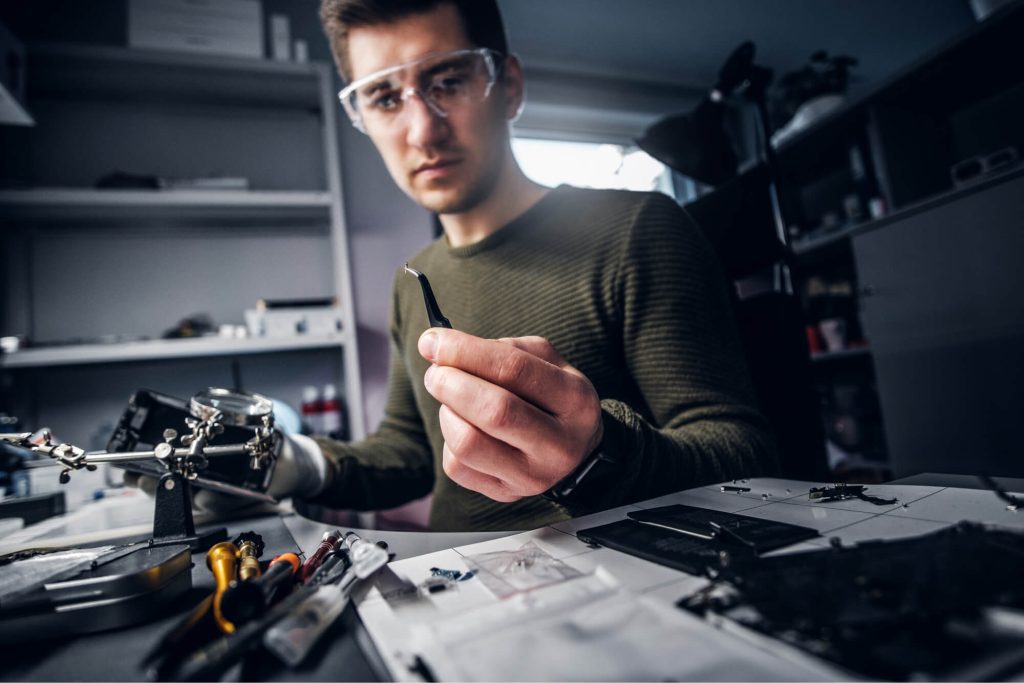
Blueberry Security specializes in analyzing digital environments at the forensic level. This includes mobile devices, laptops, servers, and cloud-based accounts. By capturing secure forensic pictures of systems, investigators can keep evidence in place without altering it, and ensure that findings remain reliable and admissible in legal proceeding.
Anyone who is facing a legal battle, a business that is dealing with an internal incident or who needs to find out the truth about an incident must perform this level of investigation.
Investigating Breaches With Precision
Cyber incidents can occur in just a few seconds however, analyzing them can be a lengthy and difficult procedure. Blueberry Security provides advanced incident response forensics to identify how breaches occur and what actions were taken by unauthorized parties.
Investigators can identify the exact time of compromise through the reconstruction of a complete timeline. They can trace the steps that follow. This includes identifying entry points and tracking malicious behavior and determining the amount of data sensitive that is accessed.
This information is valuable to companies. It not only helps resolve urgent issues, but it also enhances future security strategies. It can help individuals in situations when digital evidence is a crucial aspect of personal or legal concerns.
Becoming aware of what others miss
The detection of the hidden threat is one of the most challenging aspects of digital research. Spyware and malware are getting more sophisticated. They usually surpass traditional antivirus software. Blueberry Security focuses on uncovering the hidden threats through a deep forensic analysis.
They can spot anomalies in the system’s behavior, network activity, and file structure that may indicate an unauthorized data collection or monitoring. It is crucial to perform this analysis in highly sensitive situations such as dispute between individuals, or corporate espionage when surveillance tools can cause serious implications.
This focus on detail ensures that no evidence is missed, giving the most complete and precise picture of the circumstances.
Reporting that is Legally Ready and Expert Testimony
Digital evidence is only valuable when it is presented in a an easy and convincing way. Blueberry Security understands this and provides documentation that meets the strictest legal requirements. Their reports are structured to be understood by lawyers or judges as well as insurance providers, which ensures that their findings are turned into practical insight.
In addition, their role as an expert witness for computer-related forensics can help support cases directly in the courtroom. Professionally and in a clear manner, they present complex technical details to ensure digital evidence is understood and taken into consideration.
The combination of their technical knowledge and legal awareness makes their services particularly valuable in high-stakes litigation where precision and trustworthiness are crucial.
A trusted advisor in high-risk situations
Blueberry Security is distinguished by its dedication to dependability and quality. Each case is handled with care and attention by an experienced team consisting of U.S. based certified investigators. When it comes to delivering results it is not possible to use outsourcing or cuts and tricks.
Their experience working with major companies like T-Mobile, Raytheon, and CVS Health highlights their ability to manage complicated investigations. At the same time they are accessible to individuals and smaller organizations that require expert assistance.
Each step, starting from the initial preservation of evidence through to the final report is designed to give you clarity as well as confidence in the results.
Uncertainty could be converted into clarity
Digital threats are usually stressful, particularly when the stakes are heightened. Blueberry Security converts this uncertainty into a clear and logical conclusion. They offer solutions that are more than superficial fixes, by combining the latest technology with expert investigators.
If you have to deal with a compromised or illegal account, legal dispute or an investigation by your company using a cyber-forensics expert will ensure that you have the data you require.
In a world where electronic evidence plays an increasingly crucial role being able to have the right expert on your side can make all the difference.